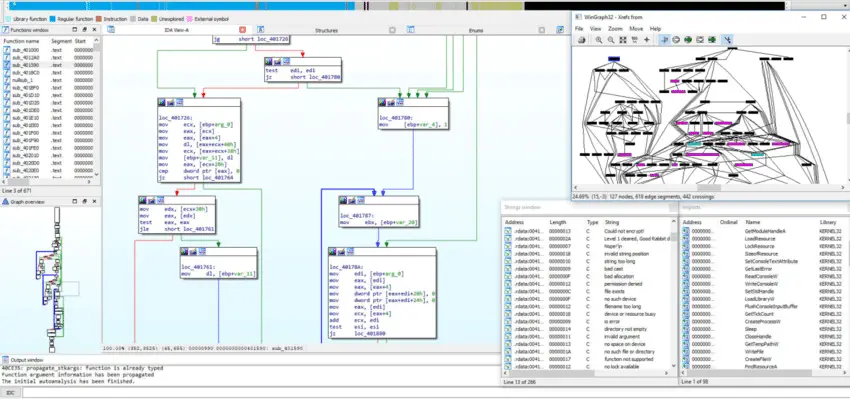
What are malware artifacts ?
In the intricate landscape of cybersecurity, understanding the concept of malware artifacts is paramount for safeguarding digital environments. All malwares has their own digitale signature that is represented by their artifacts, that can be used to detect them in infected machines. So, what are malware artifacts? Malware artifacts are traces ...