
19 best tools for cloud penetration testing
Cloud networks are become more and more used by companies. Most companies start to merge their local network to a cloud version either totally or at least partially. Hybrid use ...

Cloud networks are become more and more used by companies. Most companies start to merge their local network to a cloud version either totally or at least partially. Hybrid use ...

Performing a penetration test against an API is very similar to performing a penetration test against a web application. Both applications use web technologies and have basically the same type ...
Penetration testing is not yet a mature field like software development or network configuration. Just ten years ago, finding structured information about how you can perform penetration testing was really ...

A WAF is one of the most recommended security solutions for web applications. This solution was made to stop known and unknown attacks against websites. However, cyber security researchers have ...

Penetration testing is not an exact science, therefore having a well-defined methodology to optimize the results as required. Fortunately, many well-known organizations and researches labs have already created and published ...
After years of experience in penetration testing, I can say that one of the best things that can happen during a penetration test is to find a security misconfiguration. Unfortunately, ...
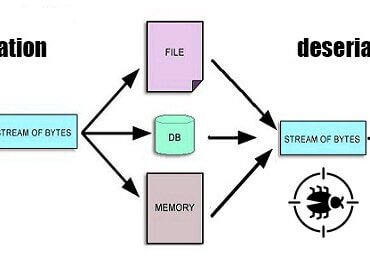
After starting to use the object-oriented development concept, new types of vulnerabilities were born. Insecure deserialization vulnerabilities were one of those vulnerabilities. Therefore, what is an Insecure Deserialization vulnerability, and ...
DDOS attacks are one of the easier and most popular attacks that can a website or server in general faces. The number and the power of those attacks are at ...

Practicing penetration testing legally was always a difficult thing to do while learning this skill. This problem did exist years ago where even the information was not so organized and ...

The internet is full of threats that are discovered each day and for years antivirus vendors were struggling to find and remove those threats before they hit their client’s machines. ...