
Website supply chain attack prevention
One of the most critical and dangerous cyberattacks that any website could be vulnerable to is the supply chain attack. Those types of attacks are very difficult to detect and ...

One of the most critical and dangerous cyberattacks that any website could be vulnerable to is the supply chain attack. Those types of attacks are very difficult to detect and ...

Over the last few years when supply chain attacks have become the main type of attacks used by hackers to penetrate systems, I’ve got a lot of questions about it ...

The XDR technology is one of the most confused not well-defined solutions that actually exist in the market. This technology has evolved from EDR and NDR to reach some SIEM ...
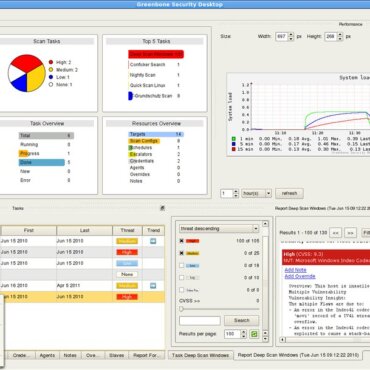
Vulnerability scanners are one of the most important tools for both security experts and developers. With the rise in the complexity of software developed around the world, using these tools ...

Vulnerability scanners are one of the best cyber security solutions that you can use to secure your network. However, one of the most known myths that I always hear about ...

When we speak about secure development and how we can speeds up the development process the first concept that gets into our head is the DevSecOps. More and more companies ...
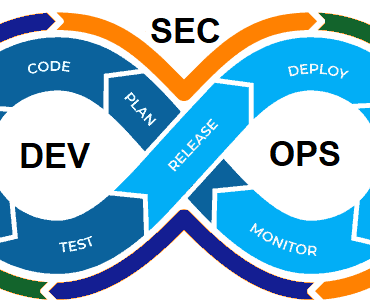
Adopting and implementing the Devsecops principles in your development process is becoming more and more important to produce secure applications. Unfortunately, by searching this subject on Google you can’t find ...

Performing a penetration test against your mobile application is becoming an important task for higher security. Unfortunately, performing a penetration test without following a well-defined methodology could waste time without ...

Fixing the discovered vulnerabilities after receiving the penetration test report is the most important process and the most time-consuming process. Therefore, one of the most common questions I get from ...

Cloud infrastructure is becoming more and more used by companies around the world. Therefore, performing a penetration test against your own cloud infrastructure or your client’s cloud is becoming so ...